Hi!
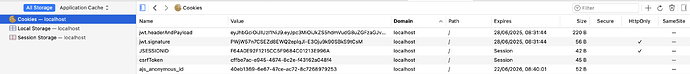
Has something changed in the CSRF handling from 24.7 to 24.8? I do not really need it since I use stateless JWT authentication for my own endpoints but since I updated from 24.7.5 to 24.8.0.beta2 I get problems after logging in into my app, apparently because the renewed CSRF token does not make it into the browser and subsequent calls to /connect/** fail. Refreshing the page after login helps, but for now I probably have to disable CSRF for /connect/**
Thanks in advance
Olaf
[nio-8183-exec-6] o.s.s.w.savedrequest.CookieRequestCache : saved request doesn't match
[nio-8183-exec-6] o.s.s.w.a.AnonymousAuthenticationFilter : Set SecurityContextHolder to anonymous SecurityContext
[nio-8183-exec-6] o.s.security.web.FilterChainProxy : Secured GET /VAADIN/push?v-r=push&debug_window&token=ad41cd95-46d5-4d3b-acbd-3b484c19f17f&X-Atmosphere-tracking-id=0&....
[nio-8183-exec-4] o.s.security.web.FilterChainProxy : Securing POST /connect/UiSettingsService/fetchUiSettings
[nio-8183-exec-5] o.s.w.r.f.client.ExchangeFunctions : [5e643950] HTTP GET http://localhost:8130/internal/v1/subscriptions/....
[r-http-epoll-33] o.s.w.r.f.client.ExchangeFunctions : [5e643950] [07da98fc-2] Response 200 OK
[r-http-epoll-33] org.springframework.web.HttpLogging : [5e643950] [07da98fc-2] Decoded [ (truncated)...]
[nio-8183-exec-5] o.s.w.r.f.client.ExchangeFunctions : [19735b97] HTTP GET http://localhost:8130/internal/v1/users/...
[or-http-epoll-9] o.s.w.r.f.client.ExchangeFunctions : [19735b97] [c4c32d30-61] Response 200 OK
[or-http-epoll-9] org.springframework.web.HttpLogging : [19735b97] [c4c32d30-61] Decoded [User(authProviderId=firebase, (truncated)...]
[nio-8183-exec-5] o.s.s.w.savedrequest.CookieRequestCache : saved request doesn't match
[nio-8183-exec-5] .s.ChangeSessionIdAuthenticationStrategy : Changed session id from FB9F373CD166885EF1A71EBE9C153699
[nio-8183-exec-5] o.s.s.w.csrf.CsrfAuthenticationStrategy : Replaced CSRF Token
[nio-8183-exec-4] o.s.s.w.savedrequest.CookieRequestCache : saved request doesn't match
[nio-8183-exec-4] o.s.s.w.csrf.CsrfAuthenticationStrategy : Replaced CSRF Token
[...]
[nio-8183-exec-2] o.s.security.web.FilterChainProxy : Securing POST /connect/UiSettingsService/getAvailableLanguages
[nio-8183-exec-2] o.s.security.web.csrf.CsrfFilter : Invalid CSRF token found for http://localhost:8183/connect/UiSettingsService/getAvailableLanguages
[nio-8183-exec-3] o.s.security.web.FilterChainProxy : Securing POST /connect/UiSettingsService/getAvailableCountries
[nio-8183-exec-3] o.s.security.web.csrf.CsrfFilter : Invalid CSRF token found for http://localhost:8183/connect/UiSettingsService/getAvailableCountries
[io-8183-exec-10] o.s.security.web.FilterChainProxy : Securing POST /connect/CurrencyService/getAvailableCurrencies
[io-8183-exec-10] o.s.security.web.csrf.CsrfFilter : Invalid CSRF token found for http://localhost:8183/connect/CurrencyService/getAvailableCurrencies
[nio-8183-exec-8] o.s.security.web.FilterChainProxy : Securing POST /connect/UiSettingsService/getAvailableTimeZones
[nio-8183-exec-8] o.s.security.web.csrf.CsrfFilter : Invalid CSRF token found for http://localhost:8183/connect/UiSettingsService/getAvailableTimeZones